AI-Powered Threat Exposure Management
Expose Attack Paths Before Hackers Do.
SafeHill SecureIQ helps security teams operationalize a hacker’s mindset by continuously proving what attackers can exploit, mapping the attack path, and turning it into a short, defensible fix-first plan.
Introducing Helix
Security validation for vibe coding.
Helix combines AI-powered code scanning, autonomous exposure validation, and agentic AI pentesting to help teams find deeper application risk, confirm real exploits, and secure modern software faster.
Press Release
SafeHill Acquires Arcane Security to Secure the Rise of Vibe Coding.
The Arcane Security acquisition strengthens SafeHill SecureIQ™ with AI-driven code analysis and continuous application security.
Trusted by teams who need proof, not noise




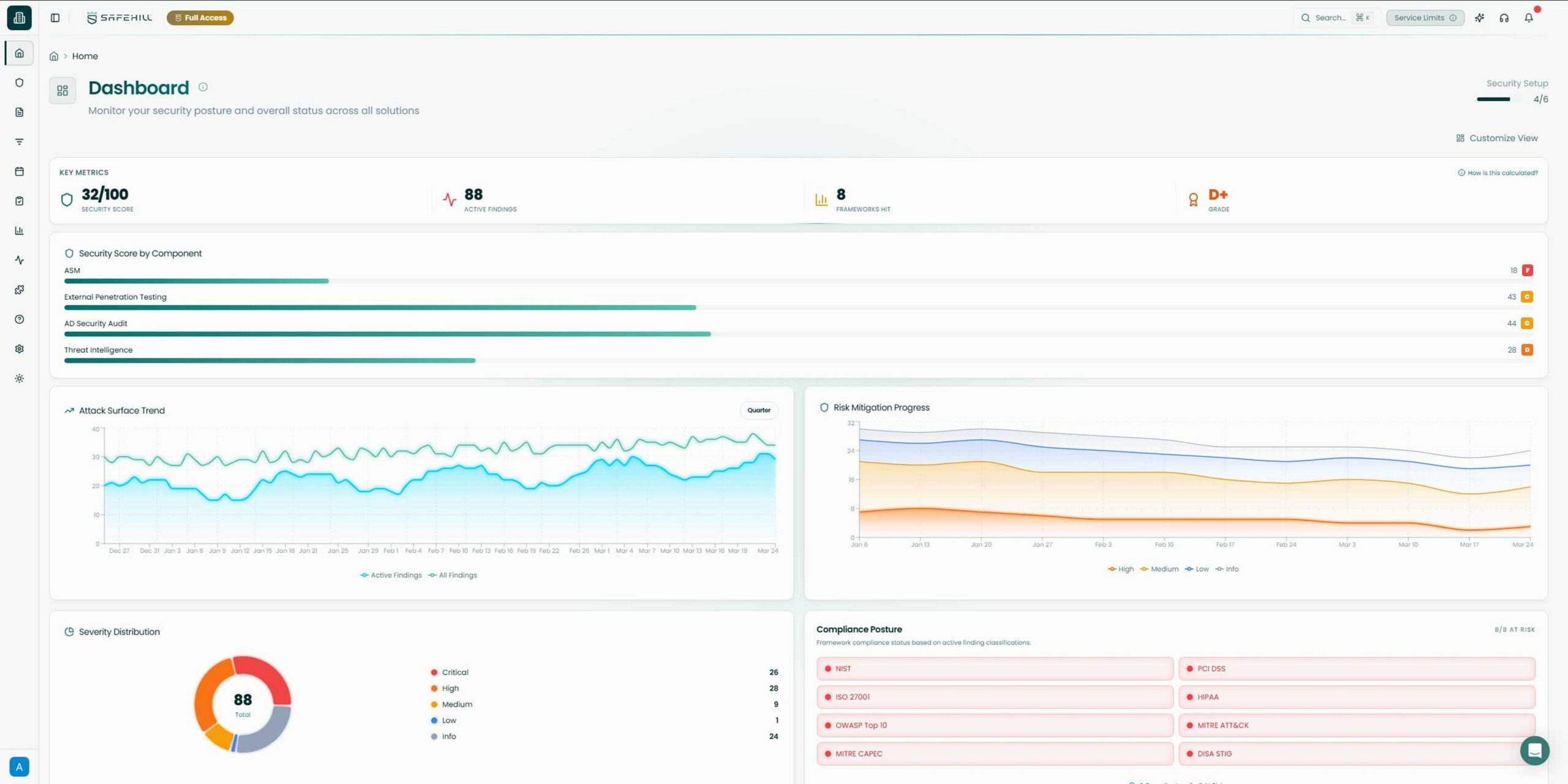
What you get with SafeHill
Not a report you file away. A living exposure story your team can act on.
Validated attack paths
A short list of real exploit sequences that lead to your crown jewels - confirmed by humans, not assumed.
Proof and evidence
Screenshots, steps, and artifacts that show true exploitability and reachability.
Prioritized remediation plan
A ranked list of fixes reviewed by humans that actually break the attack path.
Workflow-ready tasks
Jira/Slack-ready tickets with clear ownership and action steps to mobilize your team.
Retest confirmation
Evidence that the path is closed after remediation so you can defend the outcome.
Compliance and reporting
Clear mapping to frameworks and reporting that shows how remediation supports compliance progress.
The Problem?
Standard security practices can’t keep up with how attackers actually move.
You already run scanners. You already run pentests. But can you explain your top five attack paths today, without guessing?
Noise leaves teams in the dark
You get long vulnerability lists ranked by generic severity. Attackers don’t operate by severity - they operate by reachability and sequence.
Point-in-time testing falls short
Quarterly and annual pentests go stale. Environments change daily. Attackers wait for this drift to happen before they strike.
Too many tools, no unified story
Cloud, SaaS, identity, endpoints, vendors. Exposure is fragmented across systems and teams, creating overlap and complexity.
The Solution
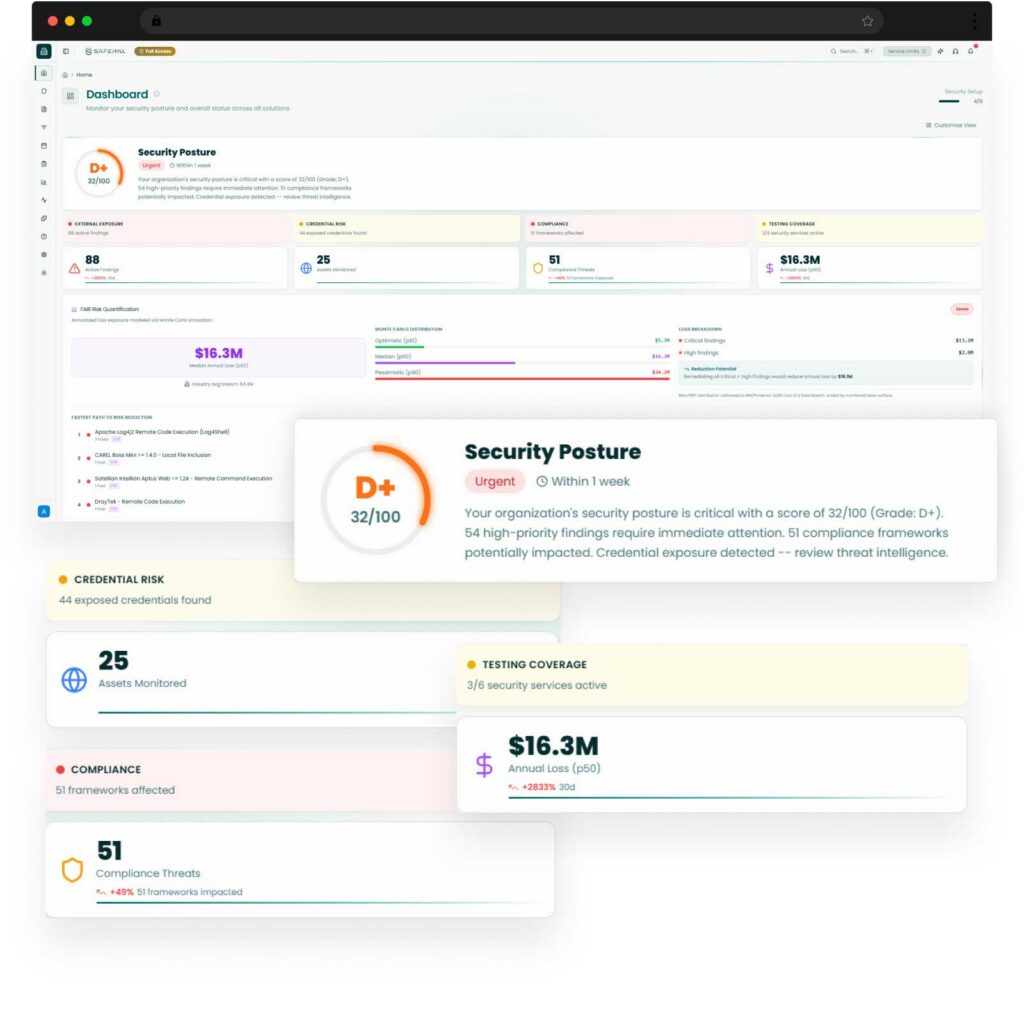
Meet SafeHill SecureIQ: Where Human Insight Meets AI Precision
Our proactive solution allows teams to continuously discover and map hidden attack paths (not just vulnerabilities), validate legitimate exploits using a dedicated team of human ethical hackers scaled with agentic AI, and prioritize remediation based on compliance and business impact.
Continuous discovery of internet-facing assets, cloud/on-prem/hybrid networks, misconfigurations, and exposed services - so you see what attackers see first.
Automation provides coverage and scale. Our expert ethical hackers validate what matters. High-risk paths come with proof, not assumptions.
We group related weaknesses into sequences and prioritize by reachability, impact, and active exploitation, not raw CVE counts.
Prioritization adjusts when the world changes: exploited-in-the-wild signals, credential leak evidence, and other emerging tactics.
Map validated exposures and remediation evidence to the frameworks you care about, without turning the platform into a compliance-only tool.
Turn noise into action with clear, prioritized remediation guidance synced into tools your engineers already use.
Our Approach to CTEM
Built by offensive experts, we’re more than a platform. We’re a Threat Exposure Management partner.
SafeHill is designed around Gartner’s Continuous Threat Exposure Management framework from the start. Our belief is that technology alone cannot guarantee you’re secure. SafeHill’s approach combines the SecureIQ TEM platform to connect scoping, discovery, validation, prioritization, and mobilization in a single loop, with a dedicated CTEM team that behaves like an extension of your own security function.
CTEM Expertise
Stand up or refine a CTEM program tailored to your size, industry, and risk profile
Offensive Intelligence
Keep humans in the loop to validate exposures, confirm exploitability, and add offensive intelligence
Exposure Translated
Turn platform insights into clear playbooks, remediation plans, and executive-ready exposure narratives
Customer Stories
More than just continuous visibility into your attack surface.
By working with SafeHill, you get a human-led partner that stays close to your environment, your risks, and your goals.
CTO @ Bandsintown
"After working with SafeHill on a penetration test, we decided to give their platform a shot and it’s been a game changer."
CISO @ First Medical
“We’ve worked with plenty of security tools, but SafeHill stood out because they combined automation with people who actually understand how attackers think.”
Cybersecurity Manager @ Alpine Health
“It was refreshing to work with a team that didn’t just hand us findings, but helped us understand what was real and what mattered most.”
Hacker & the Fed
New episodes weekly, featuring fresh cyber cases, tools, and tactics.