DynamIQ
Continuously test running applications the way attackers move.
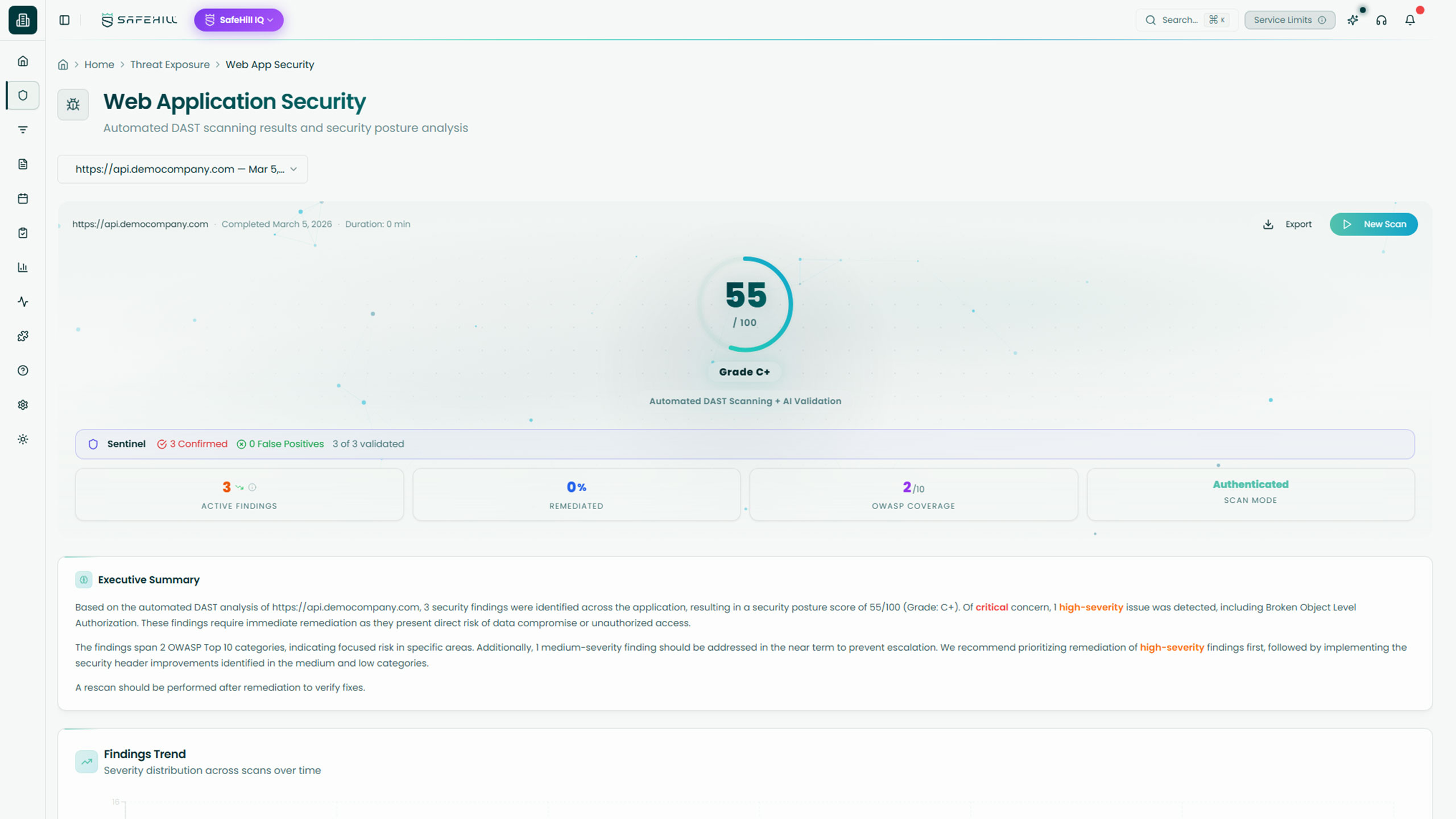
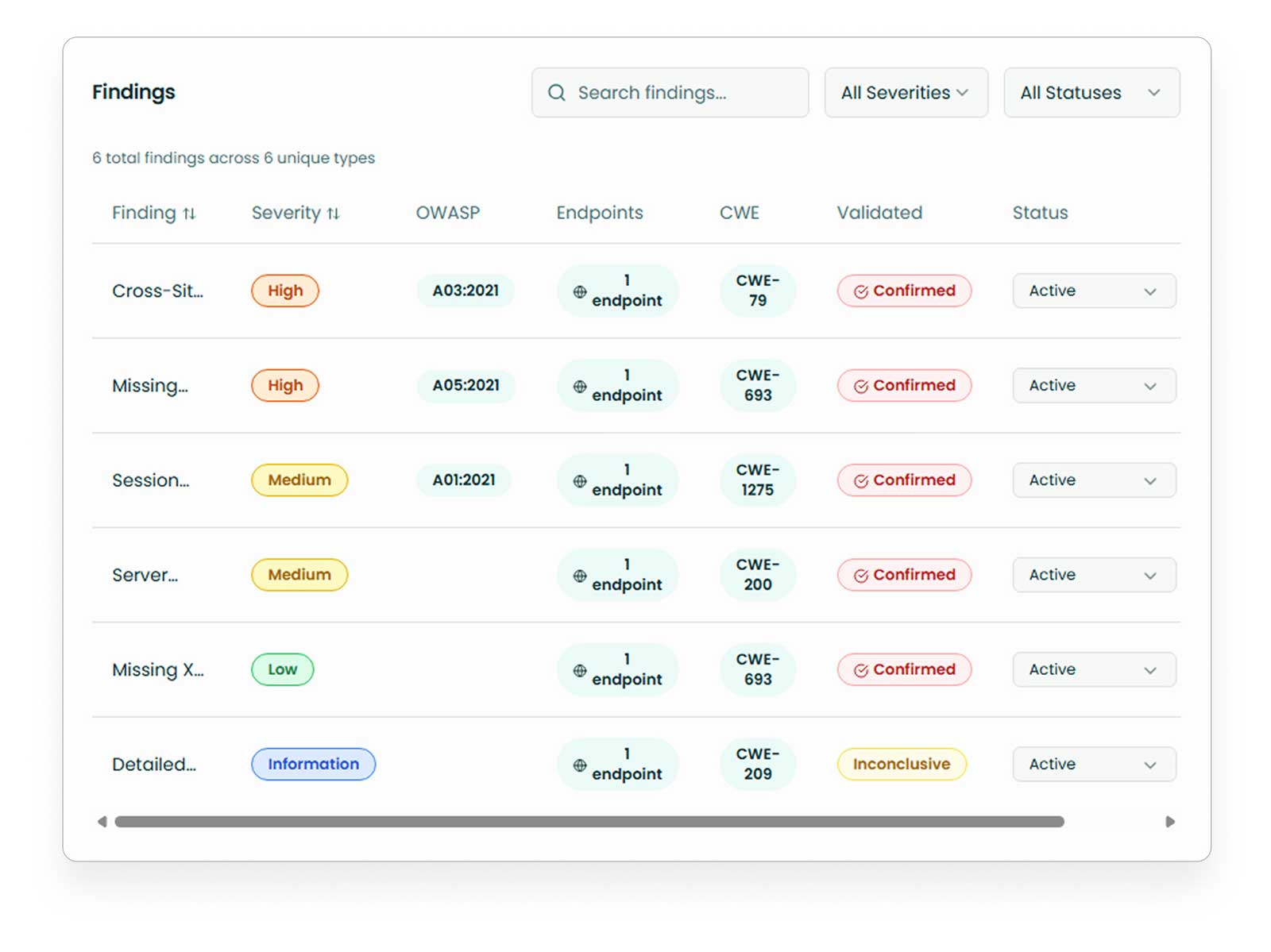
Built for modern web apps and APIs, DynamIQ combines automated dynamic testing, intelligent authentication handling, and AI-driven validation to help teams uncover exploitable weaknesses in live applications.
Continuous Validation for Running Web Apps and APIs
Many application risks surface when code is running in the real world. DynamIQ brings continuous dynamic testing to web apps and APIs, combining automated attack simulation with AI-driven validation so teams can identify exploitable weaknesses with greater confidence and less noise.

Our Stats
What our solution has done for customers
Attack Paths Discovered
Remediations Recommended
Based on real-world context and business impact.
Hours Saved
Since March 2023.
Cost Savings
By reducing tool bloat and manual testing.
Core Capabilities
Continuously test running web applications with AI-assisted workflows that simulate attacker behavior against real application logic, flows, and exposed functionality.
Key Features:
- Uses agentic AI testing to probe live web applications for runtime weaknesses and exploitable paths
- Evaluates real application behavior, inputs, and workflows rather than relying on code analysis alone
- Helps security teams assess modern applications continuously as they evolve over time
Actively test live web applications for exploitable vulnerabilities using dynamic scanning designed to surface real runtime security issues.
Key Features:
- Uses Burp Suite automated scanning to crawl and probe running applications for common and high-impact vulnerability classes
- Identifies issues such as SQL injection, XSS, SSRF, and other runtime application weaknesses
- Adds intelligent authentication handling to improve testing coverage across protected application areas
Continuously assess API endpoints and behavior to identify exploitable weaknesses that may be hidden behind application logic and authenticated flows.
Key Features:
- Tests live APIs for runtime vulnerabilities and active attack paths
- Improves visibility into application functionality that may not be fully visible in code-only review
- Helps teams validate how web and API risk behaves in real deployed environments
Confirm which findings are actually exploitable by using AI-driven validation workflows that turn dynamic findings into higher-confidence signals.
Key Features:
- Uses Sentinel’s AI-driven playbook engine to validate whether findings are genuinely exploitable
- Helps reduce false positives by separating theoretical issues from confirmed runtime risk
- Gives teams stronger evidence for prioritization and remediation decisions
Why It Matters
Where Application Risk Becomes Real
Code review and static testing are critical, but they don’t always capture how a live application behaves under real conditions. Authentication flows, runtime logic, API behavior, and complex app interactions can all introduce security issues that only become clear in execution.
DynamIQ helps teams continuously stress test live applications the way attackers would, giving them a clearer view of which weaknesses are actually reachable, exploitable, and worth fixing first.

Runtime risk does not show up in code alone
Many vulnerabilities only emerge when applications are running, handling real inputs, sessions, and workflows.
Dynamic scans need better signal
Traditional DAST tools can generate noisy findings unless teams can validate which issues are genuinely exploitable.
Modern apps and APIs change constantly
Fast-moving releases, evolving endpoints, and shifting app logic require more continuous validation than one-time testing can provide.
Outcomes
What Continuous Runtime Testing Unlocks
DynamIQ helps teams validate live application risk more clearly, reduce false positives, and focus on the weaknesses that matter most in production-like environments.
Move beyond theoretical scan results with runtime validation that confirms which application weaknesses create real exposure.
Continuously test evolving web apps and APIs so security can keep up with fast release cycles, new features, and changing attack surfaces.
Give security and engineering teams clearer signals, stronger evidence, and better prioritization for faster, more confident remediation.

How SecureIQ Works
SecureIQ combines continuous discovery, human validation, intelligent prioritization, and workflow-ready remediation into one connected process.
Discover your attack surface
SecureIQ continuously maps external assets, cloud resources, SaaS entry points, and ingests scanner data so you have a single, living view of your exposures.
Determine your testing cadence
SafeHill CTEM experts help you set and refine a testing cadence that aligns with business risk tolerance, critical assets, and budget.
Test and validate real-world attack paths
AI engines surface likely exploit chains, then SafeHill offensive experts validate what is truly exploitable and document each attack path with clear impact.
Prioritize based on business risk and compliance
SecureIQ scores and groups exposures by attacker behavior, asset criticality, threat intelligence, and maps them to frameworks like PCI DSS, CMMC, HIPAA, NIST, and ISO.
Mobilize remediation and learn from each cycle
The platform turns validated attack paths into prioritized tasks in Slack, Jira, and Datadog, tracks remediation and retesting, and feeds every cycle back into your CTEM program.
Our Approach to CTEM
How SecureIQ fits into your CTEM program
Continuous Threat Exposure Management is not a single product. A mature CTEM program combines strategy, human led cyber risk services, continuous offensive tooling, and a Threat Exposure Management platform that holds it all together.
SecureIQ is that operational hub. It sits at the center of your CTEM program and links the core CTEM pillars in a continuous loop.
Scoping and discovery
Ingests data from your environment, scanners, external attack surface monitoring, and red teaming solutions so you have one view of your threat exposure landscape.
Validation
Combines SafeHill’s human-led testing and continuous offensive tooling with AI-driven analysis to confirm which exposures are actually exploitable in the real world.
Automated Reporting
Uses business context, threat intelligence, and compliance mappings to prioritize remediation work, then pushes tasks into your existing workflows so teams can act quickly.
Cyber Services
SecureIQ + SafeHill cyber services = CTEM as a continuous mix, not a one time project
SafeHill’s cyber risk services and SecureIQ are designed to work together from day one. Your CTEM program is not just the platform and it’s not just a penetration test. It’s a living mix of human-led testing, continuous offensive tooling, and a central TEM platform that validates and prioritizes everything in one place.
Cyber risk services uncover and validate real-world risk
Continuous offensive tooling keeps coverage always on
SecureIQ centralizes, validates, and prioritizes it all
Customer Stories
See what your running applications are really exposed to
Learn how DynamIQ helps teams continuously test web apps and APIs, validate runtime exploitability, and focus on the risks that matter most.
CTO @ Bandsintown
"After working with SafeHill on a penetration test, we decided to give their platform a shot and it’s been a game changer."
CISO @ First Medical
“We’ve worked with plenty of security tools, but SafeHill stood out because they combined automation with people who actually understand how attackers think.”
Cybersecurity Manager @ Alpine Health
“It was refreshing to work with a team that didn’t just hand us findings, but helped us understand what was real and what mattered most.”