Helix
Security validation for vibe coding. Ship your code without security flaws.
Helix combines AI-powered code scanning, autonomous exposure validation, and agentic AI pentesting to help teams find deeper application risk, confirm real exploits, and secure modern software faster.
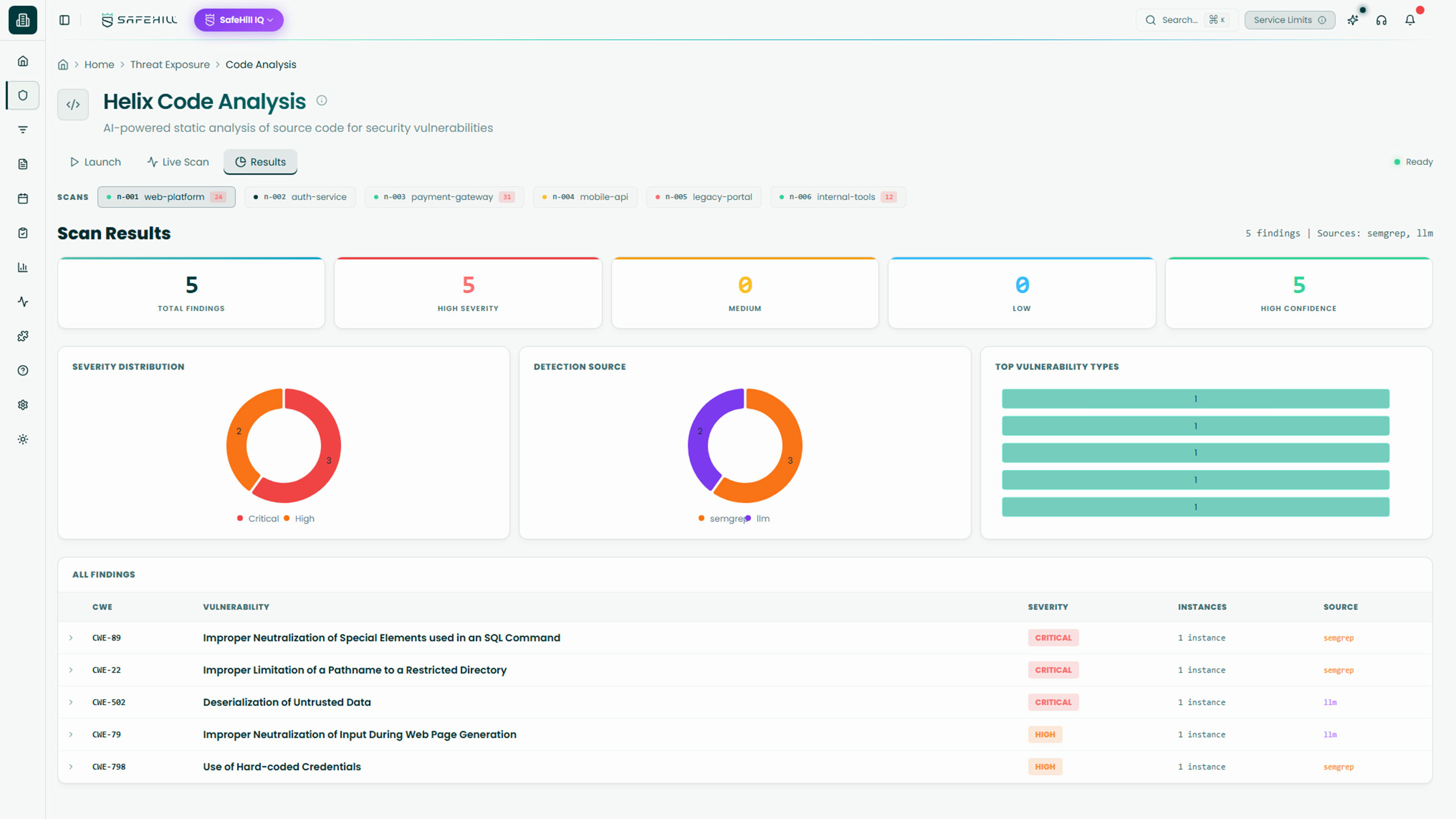
AI SAST Built for the Way Modern Software Gets Made
Helix helps teams secure modern applications with deeper code analysis, runtime validation, and AI-assisted testing that goes beyond traditional AppSec tooling. As software ships faster with AI-generated code, security teams need more than legacy scanning tools and long lists of possible issues. Helix brings together intelligent static analysis, exploit validation, and agentic testing to help teams uncover complex weaknesses, confirm what’s truly exploitable, and focus on the risks that matter most.
Our Stats
What our solution has done for customers
Attack Paths Discovered
Remediations Recommended
Based on real-world context and business impact.
Hours Saved
Since March 2023.
Cost Savings
By reducing tool bloat and manual testing.
Core Capabilities
Go beyond pattern matching with code analysis designed to uncover complex, multi-hop vulnerabilities that traditional SAST tools often miss.
Key Features:
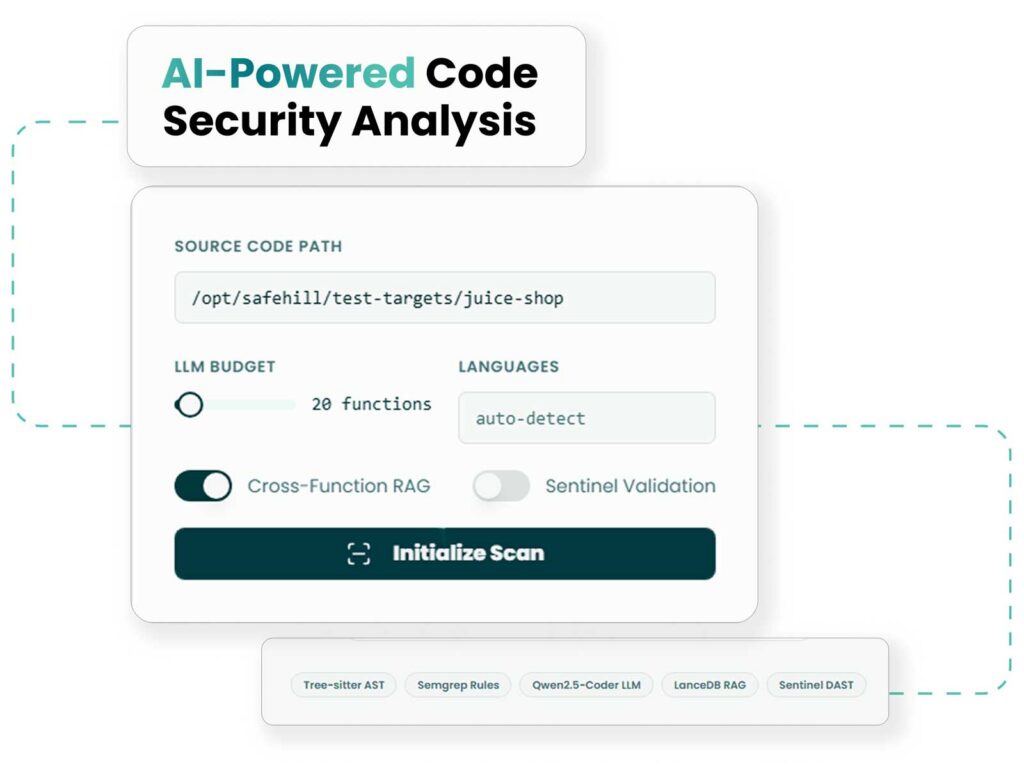
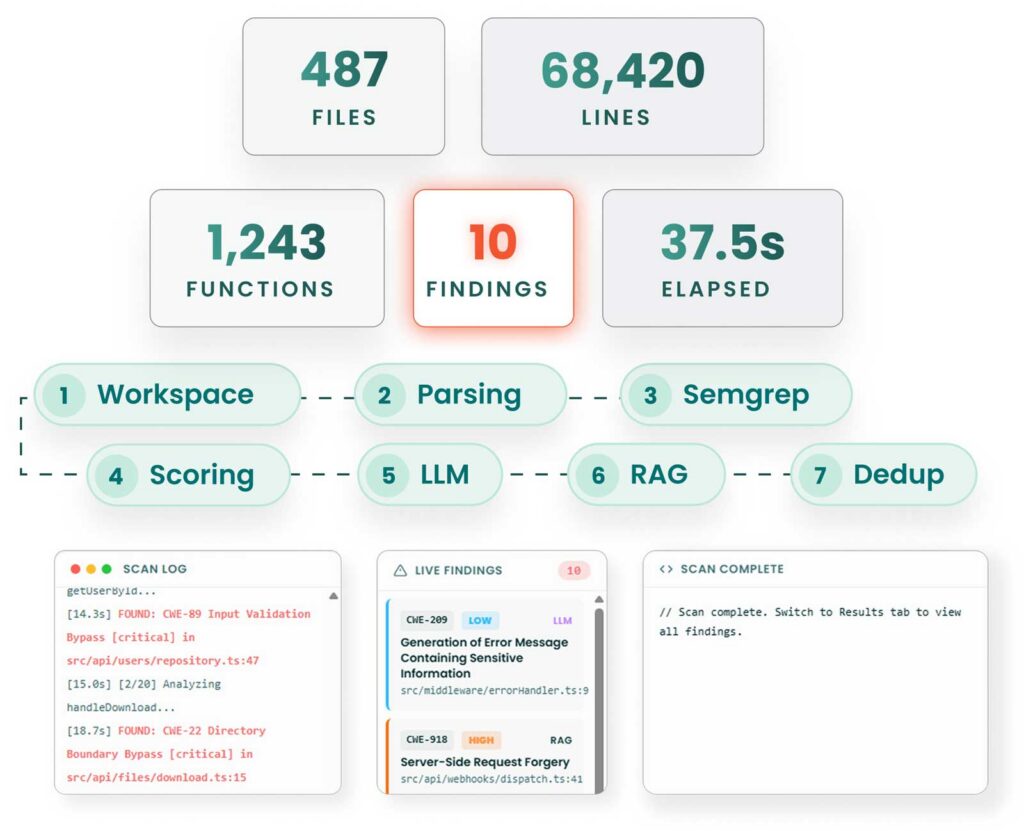
- Combines rule-based scanning, LLM-driven vulnerability analysis, code property graph taint tracking, and cross-function RAG
- Uses Tree-sitter AST parsing, Semgrep, heuristic risk scoring, and local LLM analysis for deeper code understanding
- Runs locally so code stays inside the environment with zero data leaving the network
Turn theoretical findings into confirmed threats by validating vulnerabilities against running applications.
Key Features:
- Takes static findings and executes targeted attack playbooks to test exploitability in live application contexts
- Uses a validation engine, Playwright playbook library, and Browser-Use AI agent integration to automate proof
- Helps eliminate false positives by confirming which issues are actually reachable and exploitable
Extend application security with AI-assisted testing and review workflows that help teams uncover, explore, and validate deeper application risk.
Key Features:
- Supports more adaptive testing of complex application logic and workflows
- Helps evaluate modern web apps and SaaS tools built quickly, including AI-assisted or vibe-coded applications
- Adds deeper review and exploration beyond traditional scanning outputs alone
Why It Matters
Where Modern AppSec Tools Start to Fall Behind
Today’s web apps and SaaS tools are being developed faster than ever, often with AI-assisted workflows that accelerate shipping but can also introduce hidden complexity. Traditional SAST tools are useful, but they often rely too heavily on pattern matching, generate noisy outputs, and struggle to identify vulnerabilities that span multiple functions, data flows, or runtime conditions.
Helix helps teams go further by combining deeper code analysis with runtime validation, making it easier to separate what might be vulnerable from what is actually exploitable.

Vibe-coded software adds additional flaws
Veracode found that AI-generated code introduced security flaws in 45% of tests. Modern software requires security testing that can keep up with how code is actually built today.
Pattern matching only goes so far
Traditional static tools often miss complex, multi-step vulnerabilities that span logic, context, and data flow across an application.
Too many findings end up being false positives
About 74% of scanner findings are false positives. Security teams need to know which issues are truly exploitable, not just which ones look risky on paper.
Outcomes
What Deeper Code Validation Unlocks
Helix was built for engineering teams that want security findings to live where developers already work – not in a separate ticket queue or PDF report.
Helix goes beyond basic code scanning to catch harder-to-find issues that traditional tools miss: logic flaws, injection paths, and authentication bypasses.
Validate where confirmed exploits are introduced in the running application - down to the exact lines of code.
Support modern development environments, including web apps and SaaS tools built with increasing speed and AI assistance.
How SecureIQ Works
SecureIQ combines continuous discovery, human validation, intelligent prioritization, and workflow-ready remediation into one connected process.
Discover your attack surface
SecureIQ continuously maps external assets, cloud resources, SaaS entry points, and ingests scanner data so you have a single, living view of your exposures.
Determine your testing cadence
SafeHill CTEM experts help you set and refine a testing cadence that aligns with business risk tolerance, critical assets, and budget.
Test and validate real-world attack paths
AI engines surface likely exploit chains, then SafeHill offensive experts validate what is truly exploitable and document each attack path with clear impact.
Prioritize based on business risk and compliance
SecureIQ scores and groups exposures by attacker behavior, asset criticality, threat intelligence, and maps them to frameworks like PCI DSS, CMMC, HIPAA, NIST, and ISO.
Mobilize remediation and learn from each cycle
The platform turns validated attack paths into prioritized tasks in Slack, Jira, and Datadog, tracks remediation and retesting, and feeds every cycle back into your CTEM program.
Our Approach to CTEM
How SecureIQ fits into your CTEM program
Continuous Threat Exposure Management is not a single product. A mature CTEM program combines strategy, human led cyber risk services, continuous offensive tooling, and a Threat Exposure Management platform that holds it all together.
SecureIQ is that operational hub. It sits at the center of your CTEM program and links the core CTEM pillars in a continuous loop.
Scoping and discovery
Ingests data from your environment, scanners, external attack surface monitoring, and red teaming solutions so you have one view of your threat exposure landscape.
Validation
Combines SafeHill’s human-led testing and continuous offensive tooling with AI-driven analysis to confirm which exposures are actually exploitable in the real world.
Automated Reporting
Uses business context, threat intelligence, and compliance mappings to prioritize remediation work, then pushes tasks into your existing workflows so teams can act quickly.
Cyber Services
SecureIQ + SafeHill cyber services = CTEM as a continuous mix, not a one time project
SafeHill’s cyber risk services and SecureIQ are designed to work together from day one. Your CTEM program is not just the platform and it’s not just a penetration test. It’s a living mix of human-led testing, continuous offensive tooling, and a central TEM platform that validates and prioritizes everything in one place.
Cyber risk services uncover and validate real-world risk
Continuous offensive tooling keeps coverage always on
SecureIQ centralizes, validates, and prioritizes it all
How Helix Moves from Code to Confirmed Risk
Helix reviews AI- and human-generated code before it goes live and flags security issues directly inside the developer workflow.
Launch Helix in your GitHub project
Helix is embedded directly into the development workflow as a GitHub PR reviewer – no need to add an additional window to your current workflow.
Analyze code with deeper context
When a developer opens a pull request, Helix scans the new code using a layered analysis approach that combines rule-based detections, AST parsing, taint tracking, cross-function retrieval, heuristic scoring, and local LLM analysis to uncover security flaws.
Validate exploitability at runtime with Sentinel
Sentinel takes static findings and tests them against running applications using targeted attack playbooks, helping confirm which issues are actually reachable and exploitable in practice.
Highlight findings within your code
Helix posts security findings as inline comments on the exact lines of code that matter, before a single line merges in your project.
Customer Stories
Secure your software before it goes live
Learn how Helix helps teams uncover deeper code-level weaknesses, validate exploitability at runtime, and secure modern applications with more confidence.
CTO @ Bandsintown
"After working with SafeHill on a penetration test, we decided to give their platform a shot and it’s been a game changer."
CISO @ First Medical
“We’ve worked with plenty of security tools, but SafeHill stood out because they combined automation with people who actually understand how attackers think.”
Cybersecurity Manager @ Alpine Health
“It was refreshing to work with a team that didn’t just hand us findings, but helped us understand what was real and what mattered most.”