HygenIQ
Strengthen internal security before small gaps become major paths.
Built for organizations that want deeper visibility into internal risk, HygenIQ helps organizations continuously assess internal network exposure so teams can reduce risk inside the environment, not just at the perimeter.
Built for the Risks That Live Inside the Environment
HygenIQ brings SafeHill’s AI-human hybrid approach inside the network, helping teams uncover internal weaknesses that are often missed until an attacker is already in motion. While external visibility is critical, many of the most damaging attack paths unfold after initial access. HygenIQ helps organizations continuously assess internal network posture, audit Active Directory, analyze internal attack paths, and validate the weaknesses that can enable lateral movement, privilege escalation, and deeper compromise.

Our Stats
What our solution has done for customers
Attack Paths Discovered
Remediations Recommended
Based on real-world context and business impact.
Hours Saved
Since March 2023.
Cost Savings
By reducing tool bloat and manual testing.
Core Capabilities
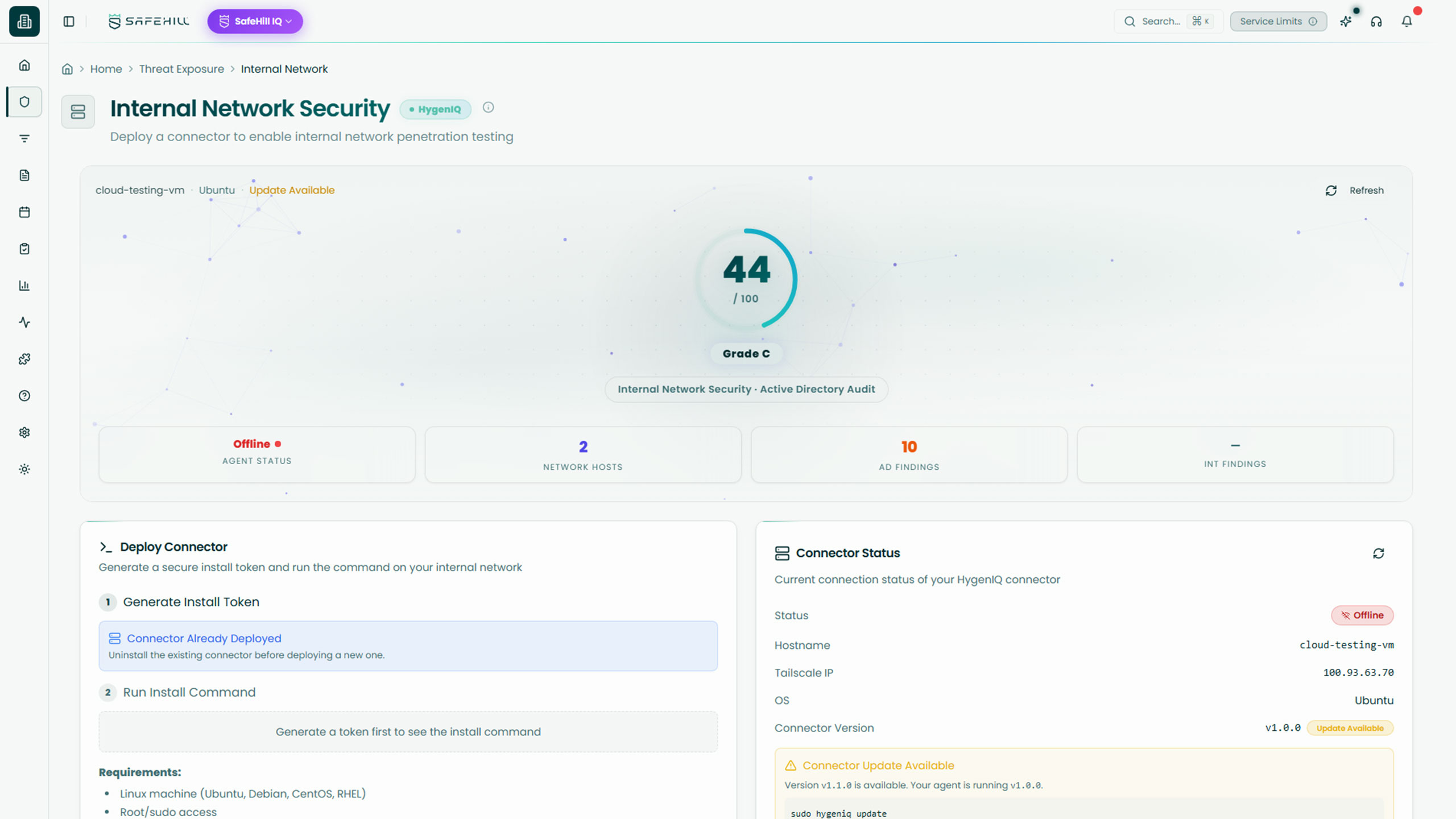
Continuously assess internal assets, systems, and network exposure to identify weaknesses that could support attacker movement inside the environment.
Key Features:
- Internal network NUC and VM deployments to extend visibility into internal environments
- Internal network agent deployment for continuous assessment and monitoring
- Asset discovery to improve awareness of internal systems and potential attack surface
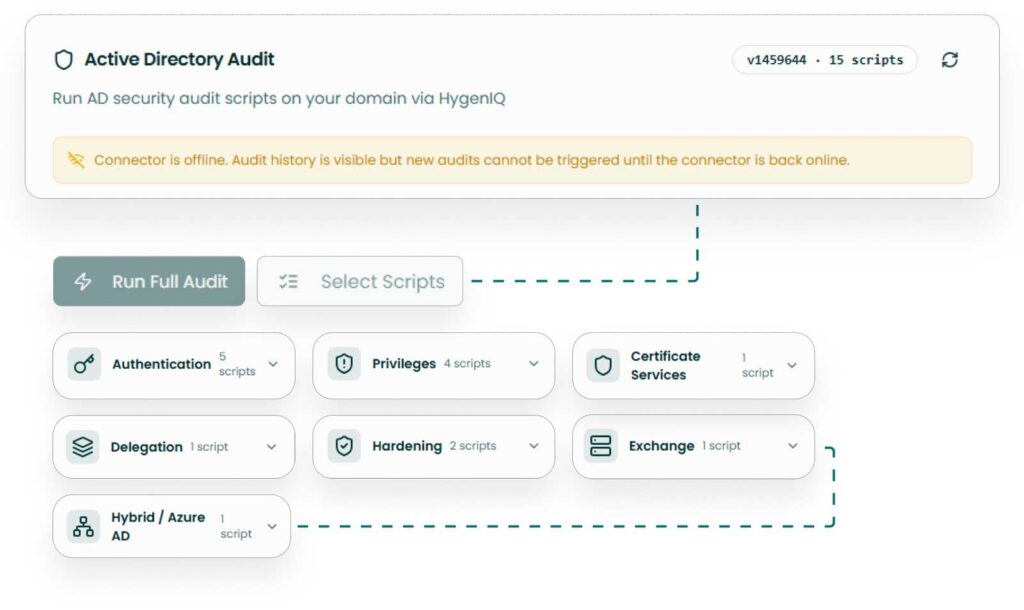
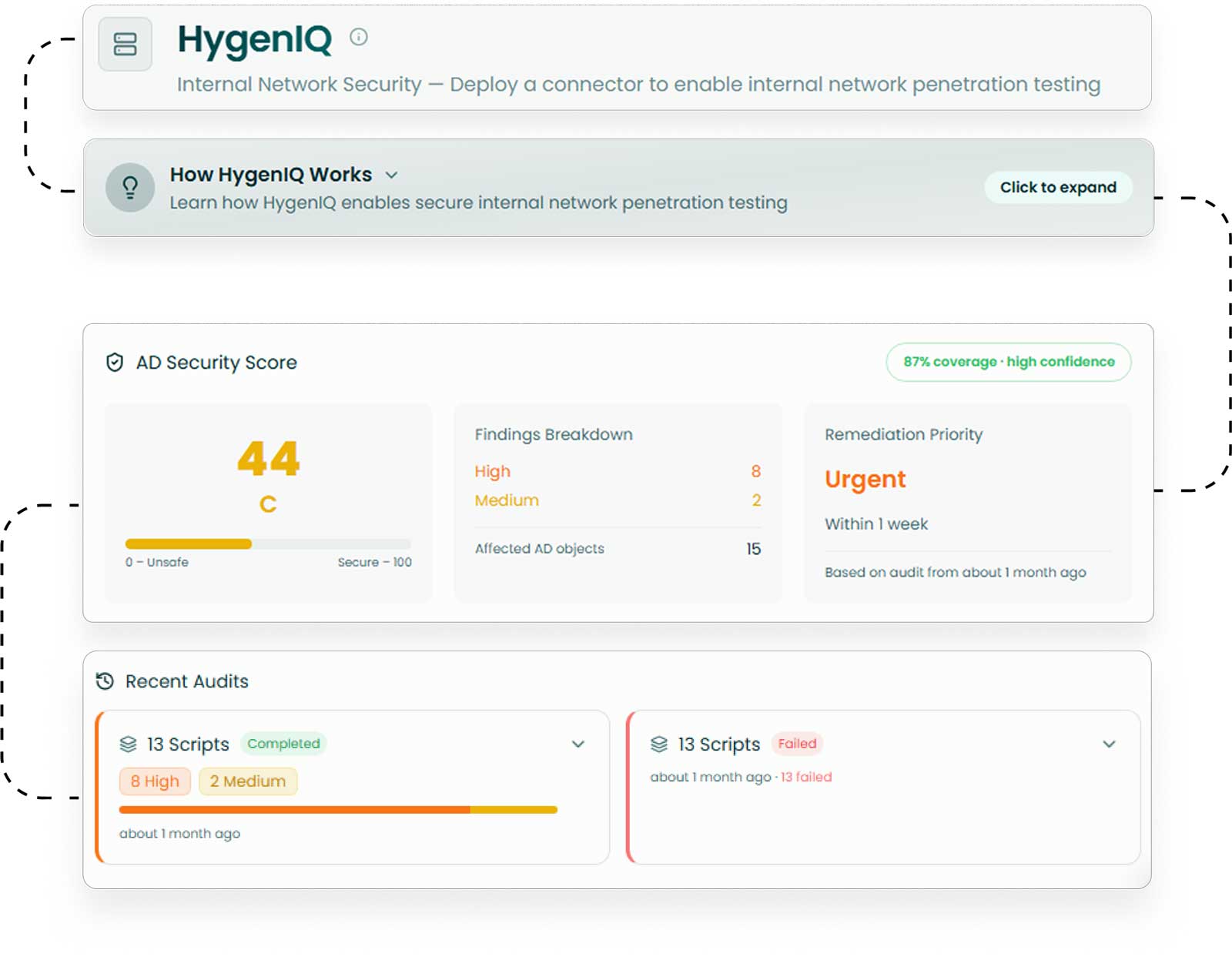
Audit and validate Active Directory continuously to uncover identity, permission, and configuration issues that can increase internal risk.
Key Features:
- Continuous Active Directory auditing and validation across critical identity infrastructure
- PKI and ADCS analysis to uncover certificate-related weaknesses and abuse opportunities
- Robust runbook system to support repeatable checks across common AD attack scenarios
Continuously test internal pathways attackers rely on to move laterally, escalate privileges, and expand access once inside the environment.
Key Features:
- Internal attack path analysis across broadcast protocols, relays, Kerberoasting, and similar techniques
- Human-guided validation of internal weaknesses that could lead to meaningful compromise
- Ongoing testing that helps teams move beyond one-time internal assessments
Why It Matters
Internal Weaknesses Often Determine How Far Attackers Can Go
Many security programs are strongest at the perimeter, but internal environments still contain the identity gaps, trust relationships, misconfigurations, and hidden pathways attackers use to expand access. Active Directory, internal network protocols, and certificate services remain some of the most valuable targets in modern intrusion chains.
HygenIQ helps teams continuously evaluate those internal conditions so they can reduce the opportunities attackers count on after initial access.
Internal weaknesses are easy to overlook
Hidden exposure inside the network can go undetected until an attacker is already using it to move laterally or escalate access.
Identity infrastructure needs constant scrutiny
Active Directory and certificate services often contain misconfigurations and trust issues that create outsized internal risk.
Point-in-time internal testing is not enough
Internal environments change constantly, which means one-time audits and occasional tests can miss the drift attackers exploit.
Outcomes
What Stronger Internal Visibility Unlocks
HygenIQ helps teams better understand internal exposure, validate meaningful attack paths, and strengthen the systems attackers rely on most after initial access.
Move beyond one-time internal assessments with more continuous validation of internal security posture.
Focus attention on the weaknesses that create the clearest path to lateral movement and privilege escalation.
Strengthen your ability to contain attacker movement by addressing the internal conditions that make expansion possible.
How SecureIQ Works
SecureIQ combines continuous discovery, human validation, intelligent prioritization, and workflow-ready remediation into one connected process.
Discover your attack surface
SecureIQ continuously maps external assets, cloud resources, SaaS entry points, and ingests scanner data so you have a single, living view of your exposures.
Determine your testing cadence
SafeHill CTEM experts help you set and refine a testing cadence that aligns with business risk tolerance, critical assets, and budget.
Test and validate real-world attack paths
AI engines surface likely exploit chains, then SafeHill offensive experts validate what is truly exploitable and document each attack path with clear impact.
Prioritize based on business risk and compliance
SecureIQ scores and groups exposures by attacker behavior, asset criticality, threat intelligence, and maps them to frameworks like PCI DSS, CMMC, HIPAA, NIST, and ISO.
Mobilize remediation and learn from each cycle
The platform turns validated attack paths into prioritized tasks in Slack, Jira, and Datadog, tracks remediation and retesting, and feeds every cycle back into your CTEM program.
Our Approach to CTEM
How SecureIQ fits into your CTEM program
Continuous Threat Exposure Management is not a single product. A mature CTEM program combines strategy, human led cyber risk services, continuous offensive tooling, and a Threat Exposure Management platform that holds it all together.
SecureIQ is that operational hub. It sits at the center of your CTEM program and links the core CTEM pillars in a continuous loop.
Scoping and discovery
Ingests data from your environment, scanners, external attack surface monitoring, and red teaming solutions so you have one view of your threat exposure landscape.
Validation
Combines SafeHill’s human-led testing and continuous offensive tooling with AI-driven analysis to confirm which exposures are actually exploitable in the real world.
Automated Reporting
Uses business context, threat intelligence, and compliance mappings to prioritize remediation work, then pushes tasks into your existing workflows so teams can act quickly.
Cyber Services
SecureIQ + SafeHill cyber services = CTEM as a continuous mix, not a one time project
SafeHill’s cyber risk services and SecureIQ are designed to work together from day one. Your CTEM program is not just the platform and it’s not just a penetration test. It’s a living mix of human-led testing, continuous offensive tooling, and a central TEM platform that validates and prioritizes everything in one place.
Cyber risk services uncover and validate real-world risk
Continuous offensive tooling keeps coverage always on
SecureIQ centralizes, validates, and prioritizes it all
Customer Stories
See what risk looks like inside the network
Learn how HygenIQ helps teams uncover internal attack paths, strengthen Active Directory hygiene, and reduce the risks attackers rely on after initial access.
CTO @ Bandsintown
"After working with SafeHill on a penetration test, we decided to give their platform a shot and it’s been a game changer."
CISO @ First Medical
“We’ve worked with plenty of security tools, but SafeHill stood out because they combined automation with people who actually understand how attackers think.”
Cybersecurity Manager @ Alpine Health
“It was refreshing to work with a team that didn’t just hand us findings, but helped us understand what was real and what mattered most.”