SecureIQ
Where Human Insight Meets AI Precision.
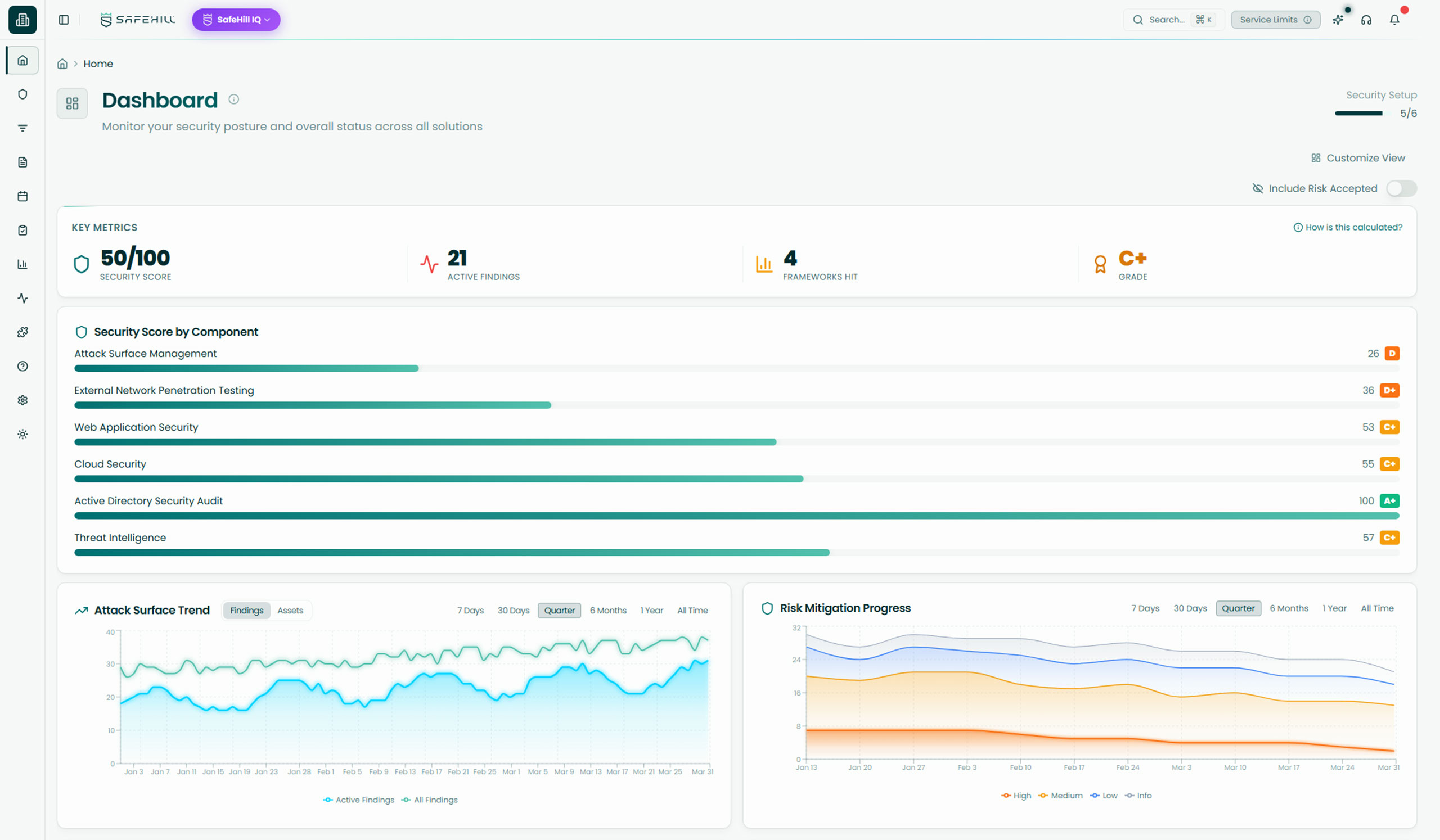
SecureIQ is our flagship AI-human hybrid threat exposure management platform, built to help teams continuously discover external risk, validate what’s actually exploitable, and prioritize what matters most.
The Platform Behind Proactive Security
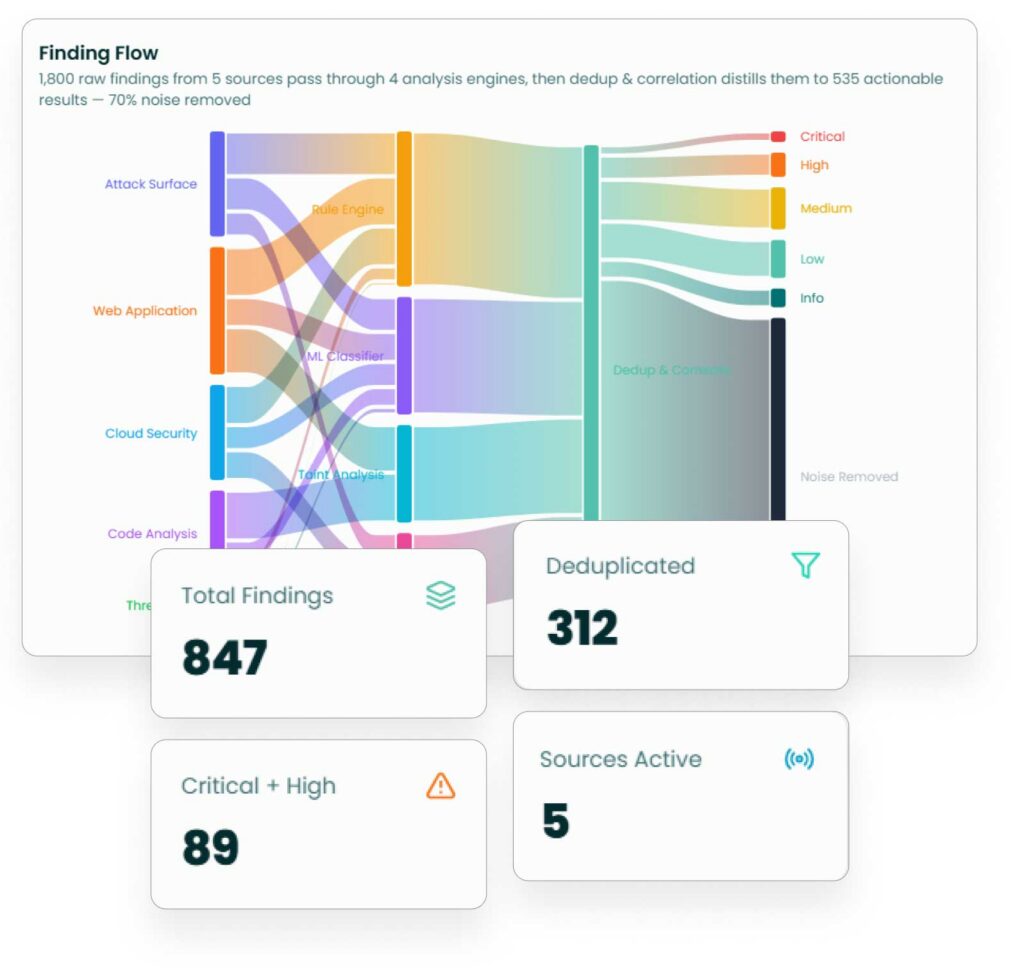
SecureIQ helps security teams move beyond fragmented tools, point-in-time testing, and long vulnerability lists by combining AI with human ethical hackers in a continuous workflow. Instead of giving teams more raw findings to sort through, SecureIQ helps uncover real external exposure, validate what matters, and bring focus to the issues that truly reduce risk.
Our Stats
What SecureIQ has done for customers
Attack Paths Discovered
Remediations Recommended
Based on real-world context and business impact.
Hours Saved
Since March 2023.
Cost Savings
By reducing tool bloat and manual testing.
Core Capabilities
Continuously discover internet-facing assets, exposed services, misconfigurations, and weaknesses so you can see what attackers see first.
Key features:
- Discovers internet-facing assets, services, subdomains, DNS records, and exposed technologies across your external environment.
- Combines active and passive reconnaissance to identify misconfigurations, exposed files, weak authentication controls, and cloud-related leak risks.
- Extends visibility with deeper web, API, TLS, and JA4 fingerprinting analysis to uncover attacker-relevant exposure signals earlier.
Pair the scale of automation with expert ethical hacker validation to confirm which paths actually matter.
Key features:
- Uses continuous and quarterly active testing to assess exposed services, login portals, DNS records, email controls, and other external entry points.
- Pairs automated coverage with US-based ethical hacker validation to confirm exploitability and reduce false positives.
- Delivers proof-backed findings that show which external weaknesses represent real risk, not just theoretical exposure.
Connect related weaknesses into real attack paths and prioritize them by reachability, impact, and exploitability.
Key features:
- Connects related weaknesses into attack paths to show how individual findings can chain together into meaningful risk.
- Prioritizes exposures based on reachability, validation, CVSS context, and real-world business impact, not raw finding volume.
- Helps teams focus remediation by ranking issues according to urgency, exploitability, and likely attacker value.
Adjust priorities as the threat landscape changes with signals tied to active exploitation, credential leaks, and emerging attacker activity.
Key features:
- Continuously monitors threat intelligence sources for exploited-in-the-wild activity, leaked credentials, and emerging attacker trends.
- Adjusts prioritization as new signals appear, helping teams respond to changing threat conditions in near real time.
- Enriches exposure data with breach and dark web intelligence to provide stronger context around urgency and risk.
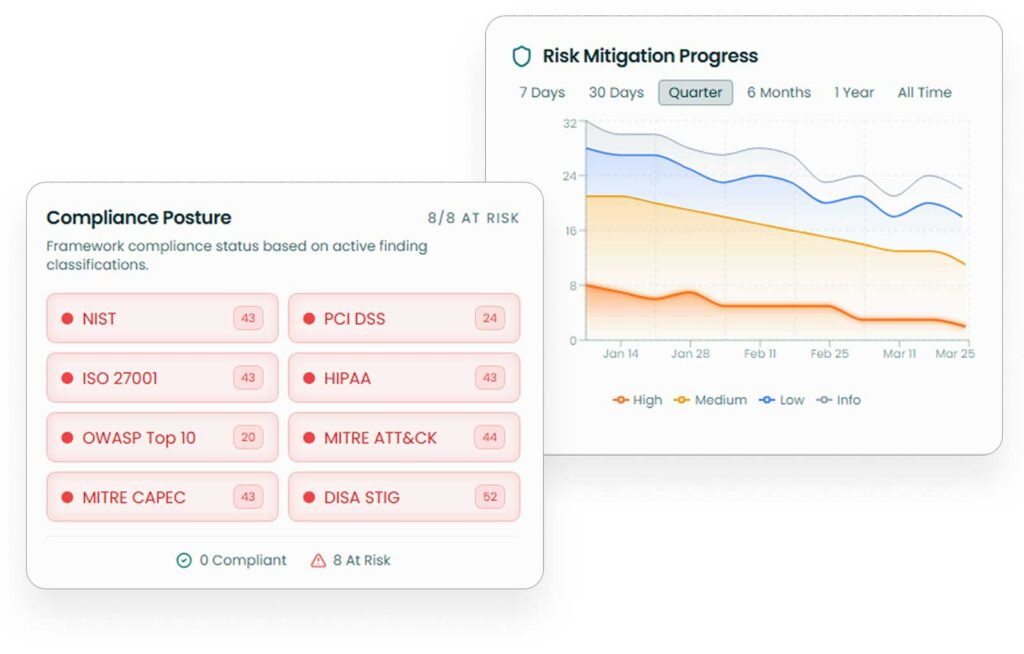
Map validated findings and remediation evidence to the frameworks your organization cares about.
Key features:
- Maps validated vulnerabilities and findings to major compliance frameworks, standards, and security taxonomies using AI-driven analysis.
- Uses natural language processing, classification, and contextual scoring to improve the relevance of framework alignment and reporting.
- Helps teams connect remediation work to audit, assurance, and governance needs without losing focus on real exposure.
Remediation Orchestration
Turn findings into clear next steps with prioritized guidance and workflow-ready integrations.
Key features:
- Translates findings into prioritized remediation guidance based on business context and validated exploitability.
- Syncs remediation steps into existing workflows through integrations with Jira, Slack, and Datadog.
- Helps teams track progress, confirm fixes, and operationalize security work across engineering, SOC, and patching teams.
Why It Matters
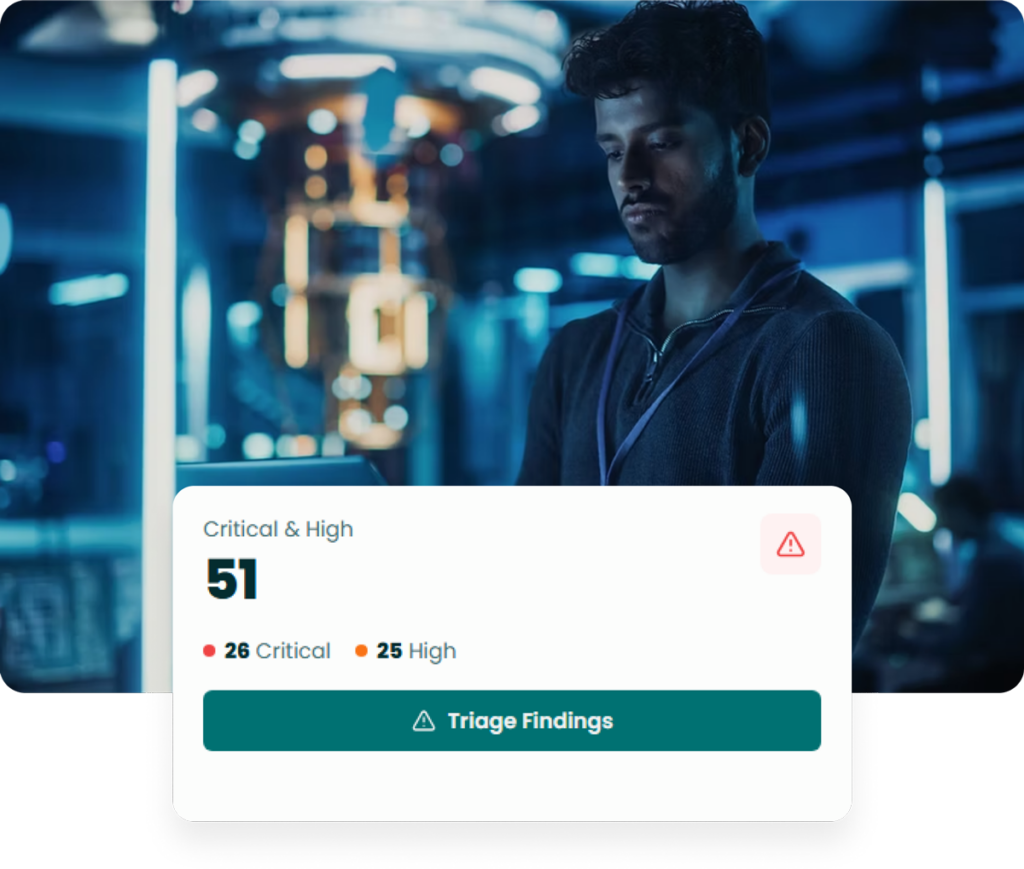
Most teams don’t need more findings, they need more clarity.
Security teams are under constant pressure to move faster, reduce exposure, and stay ahead of attackers. But traditional approaches make that difficult. Annual pentests go stale. Vulnerability scans create noise. Exposure data lives across too many tools. And severity scores rarely explain how attackers actually move.
SecureIQ helps teams shift from reactive security activity to a more continuous, validated, and understandable approach.

Point-in-time testing falls behind
Traditional assessments lose value quickly as environments change, leaving teams with outdated views of risk.
Too much noise, not enough context
Long vulnerability lists and generic severity scores make it hard to know what actually matters.
Teams need clearer decisions
Security, engineering, and leadership all need a shared understanding of what is exposed, what is urgent, and what to do next.
Outcomes
Threat Exposure Management, Reinvented
SecureIQ helps teams see real exposure more clearly, prioritize faster, and move forward with greater confidence.
Gain a clearer view of internet-facing risk, exposed assets, and the attack paths that matter most to your environment.
Focus faster on validated findings and high-risk paths so teams can spend less time sorting through noise and more time reducing risk.
Equip teams with the context, guidance, and alignment needed to remediate effectively and strengthen security over time.
How SecureIQ Works
SecureIQ combines continuous discovery, human validation, intelligent prioritization, and workflow-ready remediation into one connected process.
Discover your attack surface
SecureIQ continuously maps external assets, cloud resources, SaaS entry points, and ingests scanner data so you have a single, living view of your exposures.
Determine your testing cadence
SafeHill CTEM experts help you set and refine a testing cadence that aligns with business risk tolerance, critical assets, and budget.
Test and validate real-world attack paths
AI engines surface likely exploit chains, then SafeHill offensive experts validate what is truly exploitable and document each attack path with clear impact.
Prioritize based on business risk and compliance
SecureIQ scores and groups exposures by attacker behavior, asset criticality, threat intelligence, and maps them to frameworks like PCI DSS, CMMC, HIPAA, NIST, and ISO.
Mobilize remediation and learn from each cycle
The platform turns validated attack paths into prioritized tasks in Slack, Jira, and Datadog, tracks remediation and retesting, and feeds every cycle back into your CTEM program.
Our Approach to CTEM
How SecureIQ fits into your CTEM program
Continuous Threat Exposure Management is not a single product. A mature CTEM program combines strategy, human led cyber risk services, continuous offensive tooling, and a Threat Exposure Management platform that holds it all together.
SecureIQ is that operational hub. It sits at the center of your CTEM program and links the core CTEM pillars in a continuous loop.
Scoping and discovery
Ingests data from your environment, scanners, external attack surface monitoring, and red teaming solutions so you have one view of your threat exposure landscape.
Validation
Combines SafeHill’s human-led testing and continuous offensive tooling with AI-driven analysis to confirm which exposures are actually exploitable in the real world.
Automated Reporting
Uses business context, threat intelligence, and compliance mappings to prioritize remediation work, then pushes tasks into your existing workflows so teams can act quickly.
Cyber Services
SecureIQ + SafeHill cyber services = CTEM as a continuous mix, not a one time project
SafeHill’s cyber risk services and SecureIQ are designed to work together from day one. Your CTEM program is not just the platform and it’s not just a penetration test. It’s a living mix of human-led testing, continuous offensive tooling, and a central TEM platform that validates and prioritizes everything in one place.
Cyber risk services uncover and validate real-world risk
Continuous offensive tooling keeps coverage always on
SecureIQ centralizes, validates, and prioritizes it all
Customer Stories
Put SecureIQ to work on your environment
Book a live walkthrough with the SafeHill team to see how SecureIQ can expose your real attack paths, prioritize remediation, and support a CTEM program that fits your organization.
CTO @ Bandsintown
"After working with SafeHill on a penetration test, we decided to give their platform a shot and it’s been a game changer."
CISO @ First Medical
“We’ve worked with plenty of security tools, but SafeHill stood out because they combined automation with people who actually understand how attackers think.”
Cybersecurity Manager @ Alpine Health
“It was refreshing to work with a team that didn’t just hand us findings, but helped us understand what was real and what mattered most.”